December 18, 2022
March 7, 2018
I had class tonight…. did you?
Tuesday afternoon: media declares major NYC area snowstorm for Wednesday
Tuesday 9:17pm: I post a message to my courses Slack channel advising students that Wednesday’s 6PM class will be moved online to a zoom.us conference room. I make it clear that the course will meet even if the college closes.
Tuesday 10:13pm: 100% of students in the course confirm receipt of the message within Slack using Slacks “Simple Poll” app. That’s 100% of students confirming the message in under an hour. This was made possible due to Slacks push notification system and my amazing students.
Wednesday 10am: No snow. I go to work.
Wednesday 1pm: Snow
Wednesday 2:26pm: The college closes – canceling all remaining classes.
Wednesday 6:00PM: My PAD 713 class meets in a zoom.us online virtual room. I have 100% student attendance with everyone arriving in the room by 6:05pm. This was the first time I used the technology with these students.
What made this possible?
1) Planning
2) Funding for a zoom license (thanks student technology fee)
3) Amazing and dedicated students
October 2, 2014
3D Guns Have Now Arrived: Do we need new legislation?
I have spent the past few years researching the emerging field of 3D Printing. I presented on the topic at a NYS legislative committee roundtable. I warned at the annual meetings of both Academy of Criminal Justice Science and the American Society of Criminology that within the next 1-3 years, a viable metallic printing solution will become available. I predicted that once it does, chaos will follow. The ability to print full metallic small weapons and parts of larger weapons from home is a very dangerous ability for anyone to have. These weapons would not have serial numbers and would be untraceable.
I have been warning about it for 3 years… and now that has finally arrived.
Dubbed the “Ghost Gunner” this $1,200 device takes solid aluminum blocks and using a technology called computer-numerically-controlled milling, gradually grinds away at a solid block of aluminum until only the design is left. The process is completely computer controlled. The user just inputs the design (weapons schematics are available online) inserts a block of Aluminum and “hits” go. Many hours later a gun part made of solid aluminum emerges.
This technology has been used for years in iPhone and other electronics manufacturing. However, for the first time, the technology is being made affordable enough for home use.
(Wired Ran a Story on This Yesterday)
Here is where you can buy your very own “Ghost Gunner.”
Computer-numerically-controlled mills can make very dangerous objects. Now that they are being sold for home use manufacturing weapons without serial numbers has become easy. It is my belief that this type of technology is dangerous and should be regulated at both the Federal and State level.
One option could be to require federal registration for sale or ownership. Another policy option could require licensure for these devices.
I believe Congress and the States should pass legislation categorizing this device and institute legislation to keep these devices from being misused on a large scale.
There is not much time before thousands of these printers will be shipped around America.
I believe one was used to print this 80% Lower AR Receiver. Note: “315 In Stock.”
A possible scenario to leave you with: a criminal prints out a functioning small firearm and uses it to kill someone. The criminal can just put the firearm back in the machine that created it. The machine could then turn the murder weapon to dust.
Adam Scott Wandt, J.D., M.P.A., is an Assistant Professor of Public Policy at John Jay College of Criminal Justice, where he serves on both the Graduate faculty of the Digital Forensics and Cyber Security program and the Masters of Public Administration in Inspection and Oversight program. Professor Wandt is an Attorney and Counselor-at-Law in the State of New York.
Media requests on this issue should be sent to the attention of [email protected] with “Ghost Gunner” clearly identified in the subject line.
Professor Wandt On Twitter: @Prof_Wandt
September 21, 2014
iPhone 6 and iPhone 6 Plus
Being that my last blog was of such a serious nature… I am delighted to be blogging on something much more uplifting: The release of the iPhone 6 and iPhone 6 Plus.
I have made several different videos of varying depths: unboxing, examining, discussing, and comparing these phones.
Full 45 Minute (Six and Six Plus): Unboxing, Setup and Fist Impressions
[youtube]https://www.youtube.com/watch?v=4PDwHPQfTXI[/youtube]
Short 5 Minute (Six and Six Plus): Unboxing Only
[youtube]http://www.youtube.com/watch?v=FkDtQSe045s[/youtube]
[youtube]https://www.youtube.com/watch?v=bCJGyG0Qes8[/youtube]
August 27, 2014
Smartphone Security: Best Practices
When it comes to smartphone security, there are several “best practices” you can take to protect your data. First, be sure to always update your smartphone to the latest version of the operating system. This will ensure your smartphone receives important security updates that will help keep your data safe. Second, always use a password, even if you think you do not need one. Using a password tells the smartphone you want to keep the information safe, and most smartphones will actually handle your information/data differently than if you do not set up a password. Third, Android users should install anti-virus software. While iPhone users do not need to install anti-virus software, it is an absolutely necessity for Android users. Android users can download one of several free anti-virus programs from the Google Play store. Android users should also enable phone encryption, if supported by the phone model, which can be accessed in the “settings” menu. Android users should also make sure “USB Debugging” is disabled in the settings menu.
Finally, there is a five-step process you should engage in when you are ready to dispose of your smartphone. You should use this process no matter your method of disposal, whether you are disposing of your smartphone through a recycling program, gifting it to a friend, or selling it to someone through gazelle or e-bay, etc. Following this process will minimize the risk that others will be able to recover information/data after you wipe it.
(1) Reset your smartphone to factory default.
- Instructions for resetting iPhone: Access settings —> general —> reset —> erase all content and settings.
- Instructions for resetting Android: Varies by phone and provider. Look for “reset phone” or “reset phone to factory default” under the settings menu.
(2) Set the smartphone up again in order to access the App store (iPhone) or Google Play store (Android).
(3) Download and run a secure file shredder that will forensically wipe information from the device. I recommend the file shredder contained in a free secure communications application called Wickr. You can download Wickr from the App store (iPhone) or Google Play store (Android). Once installed, access “Secure Shredder” from the settings menu in Wickr and click “start.”
(4) Reset the phone again following the directions in step 1.
(5) Remove and keep SIM and MicroSD Cards.
While no method can absolutely guarantee your information/data is wiped completely from the phone, this proven method is a proven best practice to ensure that you keep yourself, family, friends, and co-workers safe.
WATCH THE WNBC 4 NEWS INVESTIGATIVE PIECE ON SMARTPHONE SECURITY
April 21, 2014
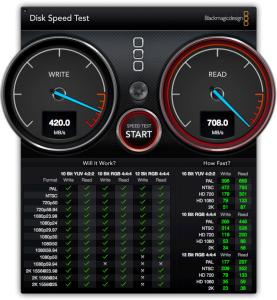
Disk Speed Test: Promise Pegasus R4 vs R6
After running disk speed tests on both the Promise Pegasus R4 and R6, we now pit them against each other in a Blackmagic speed test. Who will win?
[youtube]https://www.youtube.com/watch?v=-EGSN4cX32g[/youtube]
April 14, 2014
Disk Speed Test: Promise Pegasus R4 (RAID 5)
In this video I run a disk speed test on the Promise Pegasus R4 (RAID 5) Thunderbolt backup system using Blackmagic software.
[youtube]https://www.youtube.com/watch?v=BhQ8lIADKCU[/youtube]
April 7, 2014
Disk Speed Test: Apple Flash Storage
I ran a speed test on the Apple 751 Gb Flash Storage iMac 27-Inch Late 2012, 3.4 ghz, Intel i7 processor, 32 Gb RAM, using Blackmagic speed test software.
[youtube]https://www.youtube.com/watch?v=TwQh7hhz1tQ[/youtube]
March 31, 2014
Disk Speed Test: Promise Pegasus R6 (RAID 5)
I ran a speed test on the Promise Pegasus R6 (RAID 5) backup system. Watch the YouTube video below to see how the Pegasus stacks up.
[youtube]https://www.youtube.com/watch?v=qFqsKRNC6fo[/youtube]
March 24, 2014
Asus Google Nexus 7: YouTube Unboxing
In this unboxing we will take a look at the new Google Nexus 7 by Asus. This is the second generation Nexus 7 which was released with version 4.3 of Android Operation System. The Nexus 7 is an almost 8 inch tablet and is pretty light weight for it’s size at about 12 oz; it also comes with a 1280×800 pixel resolution screen. The Nexus has been praised for it’s price, processing, and hardware build. The tablet was criticized for a lack of rear-facing camera, and lack of expandable storage. This video goes through the unboxing of the tablet, I will release a review video soon.
[youtube]https://www.youtube.com/watch?v=DyjnwN-yspE[/youtube]